Many 2020 cybersecurity predictions were thrown out of orbit when coronavirus cases emerged and COVID-19 was declared a global pandemic by the World Health Organization in March. This year, security teams faced an uphill battle to provide remote access to enterprise networks while simultaneously protecting sensitive data from emerging, pandemic-related cyber attacks in an already […]
Archives for December 2020
2020 Work-for-Home Shift: What We Learned
The administrator of your personal data will be Threatpost, Inc., 500 Unicorn Park, Woburn, MA 01801. Detailed information on the processing of personal data can be found in the privacy policy. In addition, you will find them in the message confirming the subscription to the newsletter.
Designing Your Roadmap for Rapid Digital Transformation
While business and IT leaders are under pressure to boost their digital transformation plans, they should stop, rethink, and assess before fully diving into a roadmap. Image: metamorworks – stock.adobe.com The question all companies face today isn’t whether to embrace digital transformation, but how to best take advantage of digitalization advancements, especially considering change driven […]
Blockchain and sustainability through responsible sourcing
<!– –> Share this post: Mining for cobalt, an essential raw material for lithium-ion batteries, carries a high cost in human suffering. More than 60 percent of the world’s supply comes from the Democratic Republic of Congo (DRC), with about 45 percent coming from large-scale mining operations. The remaining 15 percent comes from small-scale mines […]
What Do We Do About Racist Machines?
We will never rid ourselves of all our biases overnight. But we can pass on a legacy in AI that is sufficiently aware of the past to foster a more just and equitable society. Enterprise AI traditionally views all data as good data. But that’s not always true. As investors think through IPOs and strategy […]
Wi-Fi: How to deploy 802.1x authentication using WPA3-Enterprise
Wi-Fi Protected Access 3 (WPA3) has brought significant security improvements to Wi-Fi networks, particularly WPA-3Enterprise, which includes tweaks to make authenticating to the network more secure. One of these is has to do with 802.1x authentication that is used to determine whether Wi-Fi clients will be granted access to the enterprise network. Wi-Fi resources Test […]
How to deploy 802.1x for Wi-Fi using WPA3-Enterprise
Wi-Fi Protected Access 3 (WPA3) has brought significant security improvements to Wi-Fi networks, particularly WPA-3Enterprise, which includes tweaks to make authenticating to the network more secure. One of these is has to do with 802.1x authentication that is used to determine whether Wi-Fi clients will be granted access to the enterprise network. Wi-Fi resources Test […]
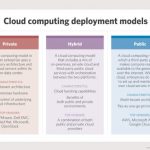
Five keys to an effective hybrid cloud migration strategy
With a hybrid cloud migration strategy, an organization extends its internal workloads into an environment that it does not own. Performance and features you know and expect from your own IT environment become dependent in part on an environment that is provided for you. The hybrid arrangement works — but you need to properly prepare […]
The software-defined home: IoT sensors can help build healthier and greener housing
Creating an oasis of health in your home is getting easier with the help of sensors and IoT devices. Image: iStock/Techa Tungateja More about IoT Business strategists at Moen, a kitchen and bathroom fixture supplier, recently identified trends that would influence future construction and home building. What they found was a theme of homes that […]
Analyzing Large Amounts of Feedback to Learn from Users
Making it easy for users to give feedback and automating the collection of feedback helps to get more feedback faster. Using artificial intelligence, you can analyze large amounts of feedback to get insights and visualize trends. Sharing this information widely supports taking action to enhance your product and solve issues that users are having. Kilian […]